SOC 2 Compliance: 2024 Complete Guide
In the ever-evolving landscape of cybersecurity and data protection, businesses are continually seeking robust frameworks to ensure the security, availability, and confidentiality of their systems. One such framework that has gained prominence is SOC 2. Let's delve into the comprehensive guide for SOC 2 compliance in 2024.
What is SOC 2?
SOC 2, or Service Organization Control 2, is a framework designed by the American Institute of CPAs (AICPA) to manage and secure sensitive information. It sets the standard for security controls that should be implemented by technology and cloud computing organizations to protect customer data.
SOC 2 compliance goes beyond the basic principles of data security; it focuses on five trust service criteria:
- security
- availability
- processing integrity
- confidentiality
- privacy.
These criteria ensure that an organization's systems are designed to keep clients' sensitive information secure and available when needed.
There are two SOC 2 types: SOC 2 Type 1 and SOC 2 Type 2. SOC 2 Type 1 evaluates whether controls are designed properly at a point of time, whereas SOC 2 Type 2 evaluates whether controls are designed and functioning as intended over a specified period of time.
An auditor is assigned to oversee the certification process. The company that conducts the audit and receives policies, controls, evidence, appoints an auditor to communicate with the company that is being audited.
Certification information is collected using the turboatlogic.com tool. It allows you to organize the work of collecting documents and other things. The parties receiving the audit and undergoing certification have access to the tool. One of the useful features is a convenient calendar and notification system.
Who Does SOC 2 Apply To?
SOC 2 compliance is particularly relevant to service providers storing customer data in the cloud. This includes Software as a Service (SaaS) companies, data center/hosting providers, and any other organization that stores customer information in the cloud. As a business analyst, it is crucial to understand that SOC 2 compliance is not limited to technology companies; any organization that manages sensitive data can benefit from adhering to SOC 2 standards.
Importance of SOC 2 Compliance
As cyber threats continue to evolve, ensuring the security of customer data has become a top priority for businesses. SOC 2 compliance provides a structured and standardized approach to managing and securing sensitive information. Beyond meeting regulatory requirements, SOC 2 compliance enhances an organization's credibility, instills trust in clients, and demonstrates a commitment to data security.
Compliance with SOC 2 standards is not only a legal obligation in certain industries but also a strategic business decision. Non-compliance can lead to reputational damage, legal consequences, and loss of business. Therefore, understanding and implementing SOC 2 compliance measures is a proactive step toward safeguarding the interests of both the organization and its clients.
Benefits of SOC 2 Compliance
Enhanced Security Measures
SOC 2 compliance necessitates the implementation of robust security measures. This not only protects customer data but also strengthens the overall security posture of the organization. By identifying and addressing potential vulnerabilities, businesses can proactively mitigate security risks.
Competitive Advantage
In an era where data breaches and cyber threats are prevalent, SOC 2 compliance sets businesses apart from their competitors. Displaying a SOC 2 certification signifies a commitment to data security and can be a crucial factor for clients when choosing a service provider.
Increased Trust and Credibility
Trust is a cornerstone of any business relationship, especially when it involves handling sensitive data. SOC 2 compliance builds trust by demonstrating that an organization has implemented stringent controls to protect customer information. This increased trust can lead to stronger client relationships and long-term partnerships.
Regulatory Compliance
Adhering to SOC 2 standards often aligns with various regulatory requirements. This ensures that organizations not only meet industry-specific regulations but also have a structured framework to adapt to evolving compliance landscapes.
Read also: Key Steps to Improve Cybersecurity in Healthcare
SOC 2 Principles
SOC 2 compliance comes in different principles, known as Trust Service Principles. These principles address specific aspects of data security and are:
- Security
The Security criterion focuses on protecting against unauthorized access, both physical and logical. It includes measures such as access controls, encryption, and monitoring to safeguard sensitive data. - Availability
Availability ensures that systems and services are available for operation and use as committed or agreed. This involves measures to prevent and minimize downtime, ensuring continuous service availability. - Processing Integrity
This criterion validates that system processing is complete, valid, accurate, timely, and authorized. It ensures that data processing is reliable and free from errors. - Confidentiality
Confidentiality involves protecting sensitive information from unauthorized access and disclosure. This includes encryption, access controls, and other measures to maintain the confidentiality of customer data. - Privacy
Privacy focuses on the collection, use, retention, disclosure, and disposal of personal information. It ensures that organizations handle personal data in compliance with privacy laws and regulations.
Collection of information and supporting documents
Information collection and supporting documents are composed of elements such as Policies, Controls, and Evidence Tasks.
SOC 2 Policies
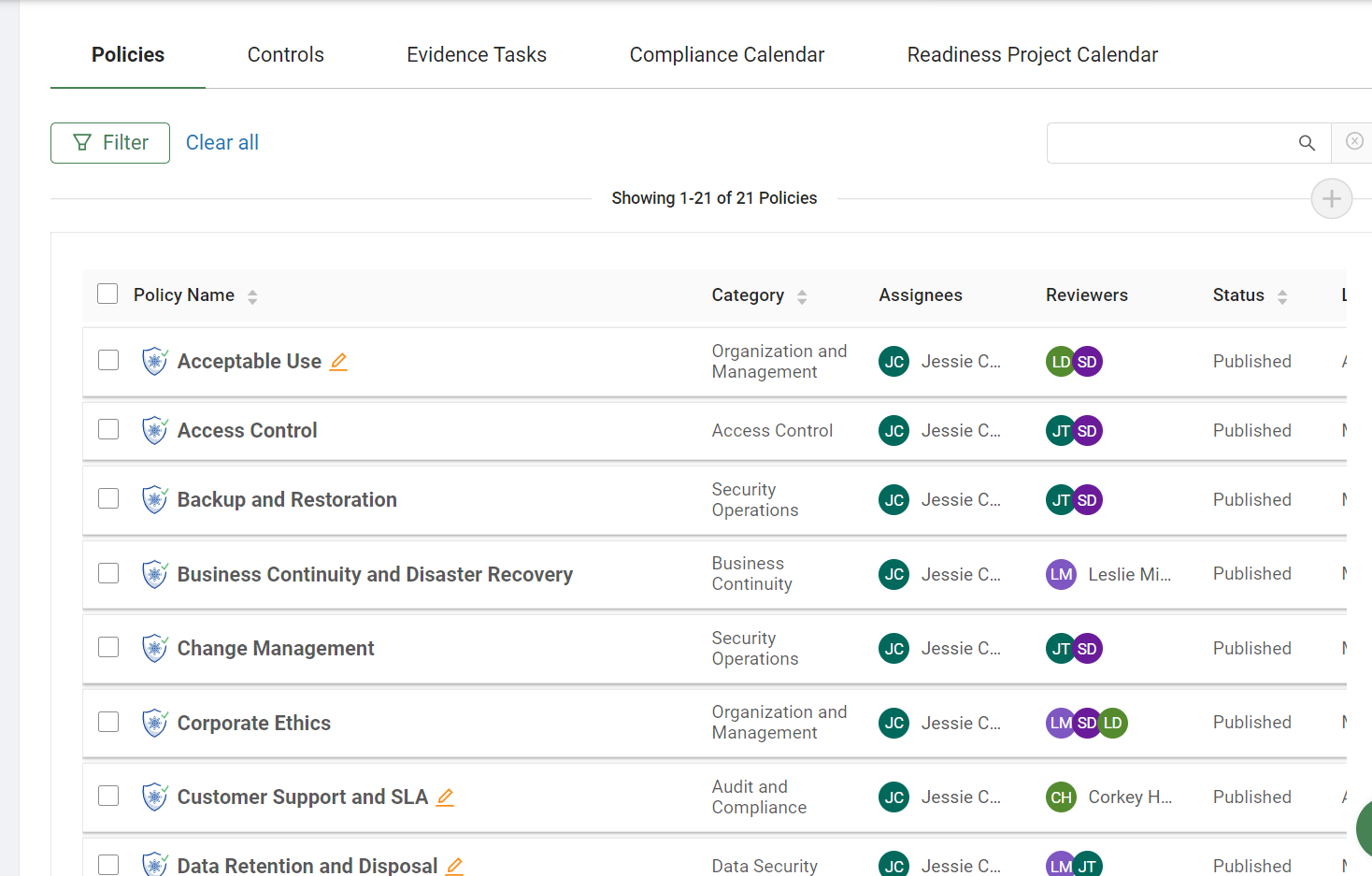
SOC 2 policies establish a document/framework for implementing data security. These policies act as fundamental requirements for the organization's employees and third-party vendors to help them meet these requirements.
List of SOC 2 Policies
- Acceptable Use Policy
- Information Security Policy
- Access Control Policy
- Information, Software, and System Backup Policy
- Business Continuity Policy
- Logging and Monitoring Policy
- Change Management Policy
- Physical Security Policy
- Confidentiality Policy
- Password Policy
- Code of Conduct Policy
- Remote Access Policy
- Data Classification Policy
- Risk Assessment and Mitigation Policy
- Disaster Recovery Policy
- Software Development Lifecycle Policy
- Email/Communication Policy
- Vendor Management Policy
- Encryption Policy
- Security Policy
- Incident Response Management Policy
SOC 2 Controls
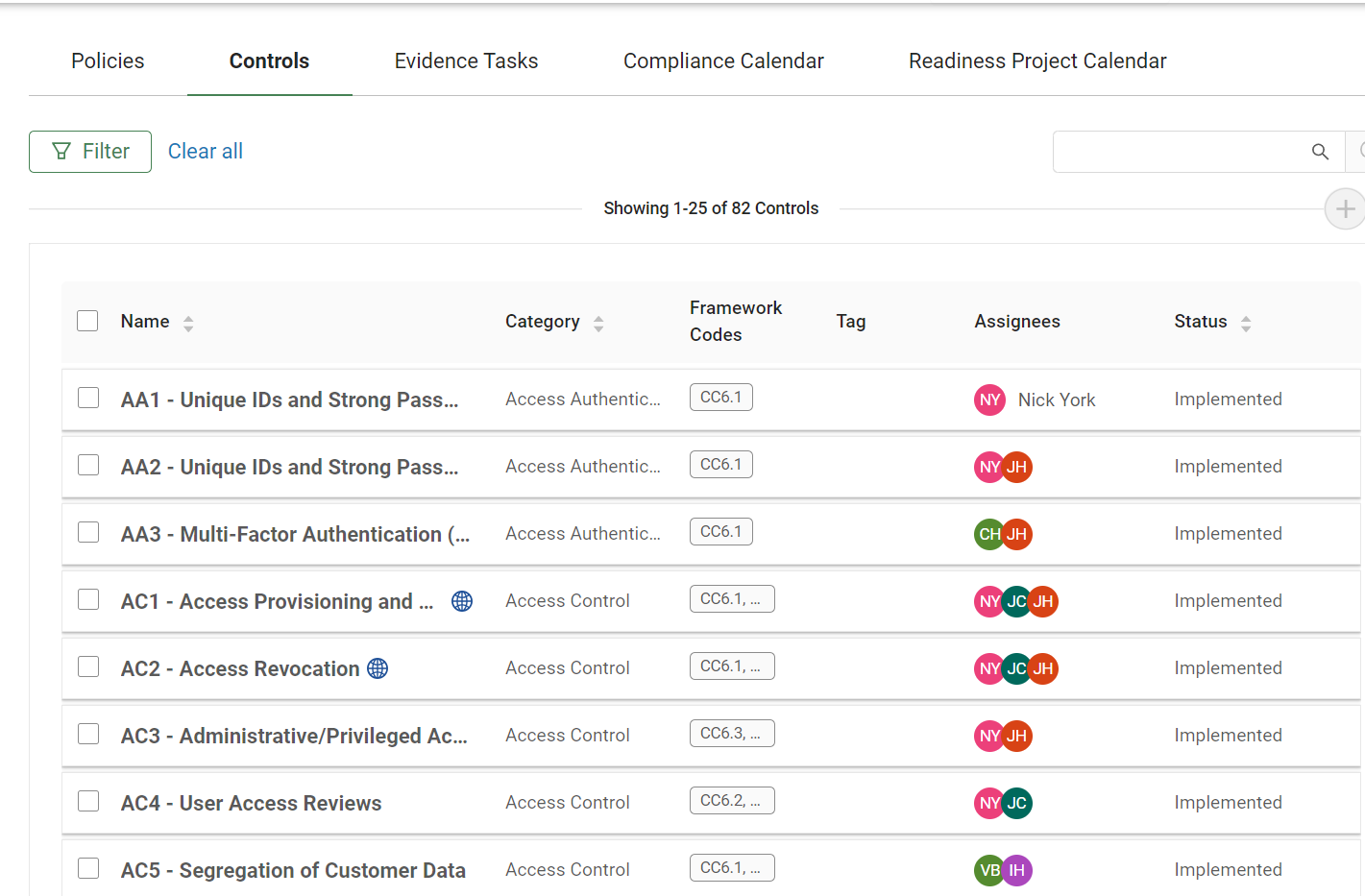 SOC 2 compliance involves implementing a set of controls to meet the criteria outlined in the Trust Service Criteria. The controls associated with the common criteria include common general IT controls. These controls can be categorized into:
SOC 2 compliance involves implementing a set of controls to meet the criteria outlined in the Trust Service Criteria. The controls associated with the common criteria include common general IT controls. These controls can be categorized into:
- Administrative Controls
These controls involve the policies and procedures implemented by an organization to ensure the proper management and governance of its systems. This includes risk management, training, and incident response procedures. - Technical Controls
Technical controls encompass the measures put in place to secure systems and data. This includes access controls, encryption, network security, and system monitoring. - Physical Controls
Physical controls are measures that restrict access to physical locations containing sensitive information. This includes security measures such as biometric access controls, surveillance, and environmental controls.
SOC 2 Evidence
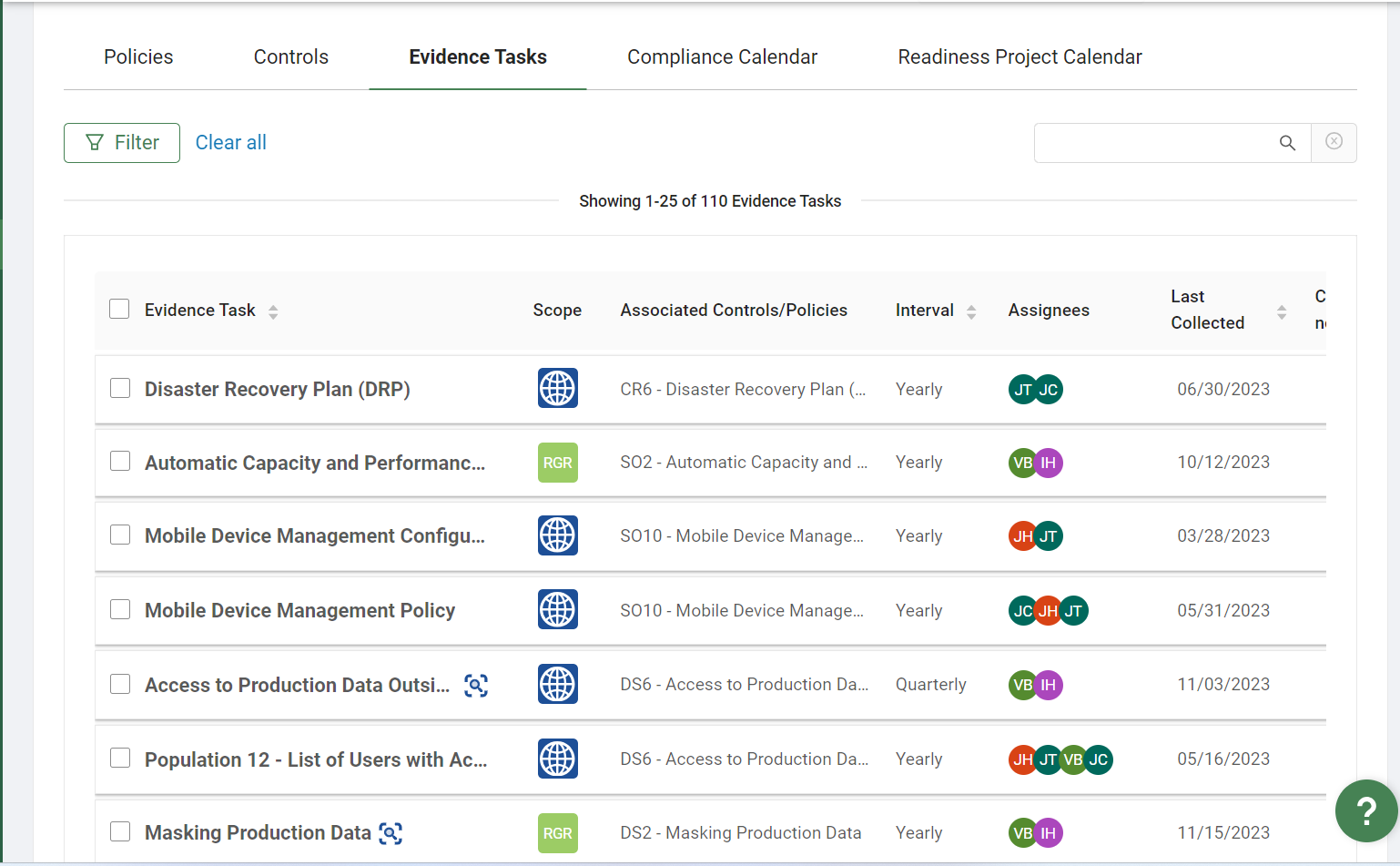
Since an audit is performed on a specific system, it is necessary to be able to verify and prove which system was used for the extraction. The processing of clients and data in a production environment is what makes it the focus of the audit. There is no point in providing documentation and processes that occur in quality control.
The second important point is the type of audit evidence. To eliminate any suspicion of manipulation, they resort to the following practices:
- Check the number of records in the source system before extracting the file and compare it with the number of records in the extracted and loaded file;
- Ability to demonstrate the source of the listing. Passing the list through another system will be a source of manipulation, and to avoid this, it is better to export the data directly from the source system.
Gathering evidence will be easier for you if you become familiar with the features of an audit.
SOC 2 Certification
Achieving SOC 2 compliance involves a thorough examination of an organization's systems and processes by an independent third-party auditor. The audit evaluates the implementation of controls, adherence to policies, and overall compliance with SOC 2 criteria.
The certification process typically involves the following steps:
- Pre-Assessment
Before the formal audit, organizations often conduct a pre-assessment to identify potential areas of non-compliance. This allows them to address issues proactively and improve their readiness for the official audit. - Formal Audit
The formal audit is conducted by an independent auditor who assesses the organization's controls and processes against the chosen Trust Service Criteria. The auditor reviews documentation, interviews key personnel, and examines evidence of control effectiveness. - Remediation
If any issues are identified during the audit, organizations must take corrective action to address these concerns. This may involve refining processes, implementing additional controls, or addressing documentation gaps. - Issuance of SOC 2 Report
Upon successful completion of the audit and remediation process, the organization receives a SOC 2 report. This report is a valuable asset that can be shared with clients, partners, and other stakeholders to demonstrate compliance with SOC 2 standards.
Company with Experience in SOC 2
SOC 2 compliance is a critical component of an organization's data security strategy. By understanding the intricacies of SOC 2, companies can proactively implement measures to protect customer data, build trust, and stay ahead in an ever-changing digital environment. As data security continues to grow in importance and SOC 2 compliance remains a valuable investment for organizations seeking to protect sensitive information, the SDH team has in-depth experience in passing SOC 2.
We assist and accompany our clients on their certification journey, covering all issues on development processes, DevOps, infrastructure, communication, project management etc. One of our recent cases is completing certification for a US-based cloud-based LMS with 470,000 students.
Write to us to get a consultation on SOC2!
Categories
Share
Need a project estimate?
Drop us a line, and we provide you with a qualified consultation.




