Digital Sovereignty Consulting and Implementation Services
The New Standard in Digital Autonomy.
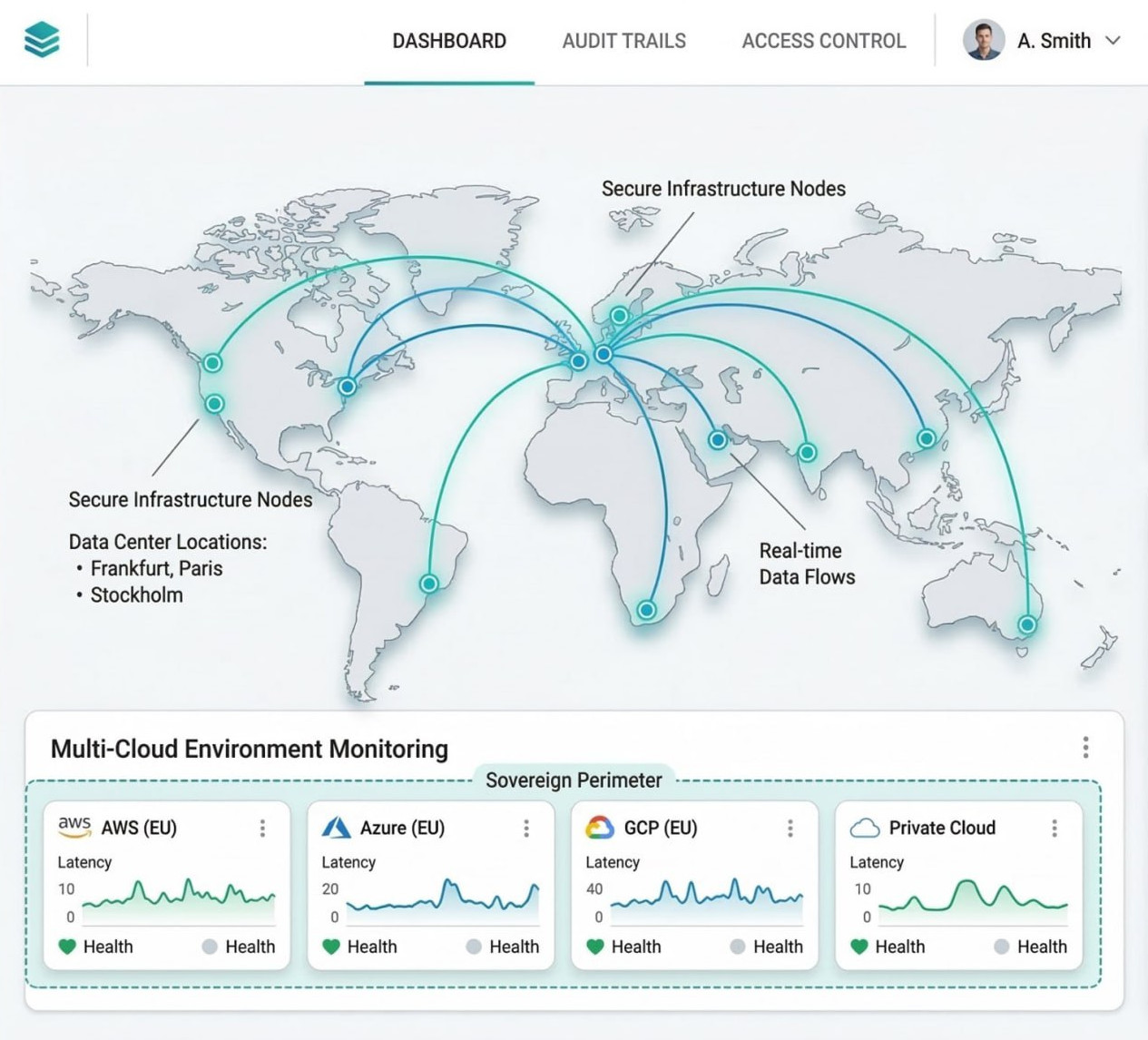
We help engineering teams design vendor-independent architectures that are exit-ready, multi-cloud compatible, and aligned with EU AI Act, DORA, and NIS2. From Kubernetes infrastructure to private LLM platforms — we build sovereign digital systems focused on code, automation, and real engineering outcomes.
Software Excellence
Building Sovereign Solutions
Level Engineering Team
& System Monitoring
What We Mean by Digital Sovereignty
Digital sovereignty is the degree of control your organization keeps over its data, infrastructure, software choices, and AI systems. It is not only about compliance. It is about maintaining technical independence, operational flexibility, and long-term strategic control.
Data Sovereignty
Full control over where data is stored, processed, and accessed, with clear jurisdictional boundaries and reduced exposure to external legal risks.
Architecture Sovereignty
Cloud-agnostic infrastructure built on portable components such as Kubernetes, Terraform, and open standards, so you can switch providers without major rewrites.
AI Sovereignty
Private AI systems, self-hosted inference, controlled model usage, and protection of training data, prompts, embeddings, and inference logs.
Operational Sovereignty
Independent operations with observability, zero-trust access, policy-as-code, auditability, and governance embedded directly into delivery pipelines.
Our Digital Sovereignty Services
From architecture strategy to full engineering implementation, we help organizations build independent, compliant, and future-proof digital platforms.
Sovereign Cloud Architecture
Design of cloud-agnostic platforms using Kubernetes, Terraform, and open infrastructure patterns to eliminate long-term vendor lock-in.
Cloud Migration & Multi-Cloud
Migration of applications, infrastructure, and data into multi-cloud environments with clear exit strategies and infrastructure-as-code automation.
MigrationSovereign AI Platforms
Private AI systems, RAG pipelines, vector databases, and self-hosted LLM inference designed to keep training data and models under your control.
DevOps & Infrastructure Automation
CI/CD pipelines, infrastructure-as-code, and policy-as-code automation integrated directly into engineering workflows.
Managed DevOpsCompliance Engineering
Architecture and technical implementation aligned with EU AI Act, DORA, NIS2, and GDPR requirements.
Legacy System Modernization
Refactoring legacy systems into scalable, cloud-native platforms while maintaining full control over infrastructure and data.
TrasformationWhy Digital Sovereignty Matters Now
Regulatory pressure, cloud dependency, and geopolitical uncertainty are turning digital sovereignty into a practical engineering priority for modern organizations.
Vendor Lock-in
Proprietary cloud services, APIs, and managed platforms can turn growth into migration debt and make future exits expensive and slow.
AI and Data Control
Training data, inference logs, prompts, and embeddings require stronger governance as AI systems become core business infrastructure.
Compliance and Resilience
EU AI Act, DORA, NIS2, and related regulations demand traceability, operational resilience, and better control over third-party dependencies.
Our Sovereign-by-Design Engineering Approach
We design and build vendor-independent systems where infrastructure, data, and AI pipelines remain under your full operational control. Our methodology combines architecture strategy, engineering execution, and compliance automation.
1. Sovereignty Assessment
Architecture review, dependency analysis, and identification of vendor lock-in risks across infrastructure, data flows, and AI pipelines.
2. Architecture Blueprint
Multi-cloud and cloud-agnostic architecture design using Kubernetes, Terraform, and open-standard components.
3. Sovereign AI Infrastructure
Private AI platforms, self-hosted inference, RAG pipelines, and vector databases designed to protect training data and model usage.
4. DevOps & Automation
Infrastructure-as-code, CI/CD automation, and policy-as-code governance embedded directly into engineering workflows.
5. Compliance Engineering
Technical implementation of EU AI Act, DORA, NIS2, and GDPR requirements directly inside architecture and deployment pipelines.
6. Implementation & Handover
Full deployment, operational documentation, and knowledge transfer to ensure long-term architectural independence.
Key Business Benefits
Complete Data & IP Control
Protect sensitive information from external jurisdictions and access risks.
Regulatory Fine Avoidance
Proactive compliance reduces legal and financial exposure.
True Vendor Independence
Switch providers without costly rewrites — thanks to open, portable designs.
Private AI & Model Sovereignty
Deploy private LLMs, RAG pipelines, and self-hosted inference. Maintain absolute ownership of your training data, embeddings, and prompts without telemetry leakage.
Operational Resilience
Design multi-cloud and hybrid architectures that withstand regional outages, geopolitical shifts, and changing cloud policies without operational downtime.
German Engineering
Bespoke software developed by SDH IT GmbH in Hamburg. Engineered for mission-critical reliability.
What Our Clients Say



They consistently lead us towards what yields in the long-term with flexibility, rather than a short-term easy fixes.
Software Development Hub has led around 30 development projects a year. Their careful development and rigorous testing have also led to bug-free deployments already. Moreover, they are praised for their friendly, efficient, and prompt attitudes throughout the engagement.

Get Started with Digital Sovereignty
A practical, engineer-led first step toward full digital autonomy for your enterprise.
Schedule a Free Assessment
Review of architecture, data flows, dependencies, and compliance gaps.
Discuss Custom Solutions
Tailored multi-cloud/hybrid plan aligned with your business and risk profile.
Define a Roadmap
Outline a realistic implementation approach, scope, and next actions — without sales pressure.
Free assessment. No obligation. Engineering discussion, not a sales pitch.
