5 Healthcare Software Cybersecurity Breaches in 2022 in the U.S. (up-to October 31, 2022)
Cybercrime brings many new victims as the number of Internet users around the world increases every year and the deployment of modern technology affects various industries.
According to an annual report by IBM Security and the Ponemon institute, the cost of data breaches in the healthcare industry has increased by 42% since 2020. For the 12th consecutive year, the healthcare industry has the highest average cost of data breaches of any industry. The average total cost of a breach in the healthcare industry amounts to $10.10 million.
Section 13402(e)(4) of the HITECH Act requires to disclose publicly a list of breaches of unsecured protected health information affecting 500 or more individuals. Over 700 healthcare organizations reported a breach of 500+ patient records in the U.S. in 2021.
There are 523 submitted breaches at this point that potentially affected 39315279 individuals, which has already exceeded last year's totals.
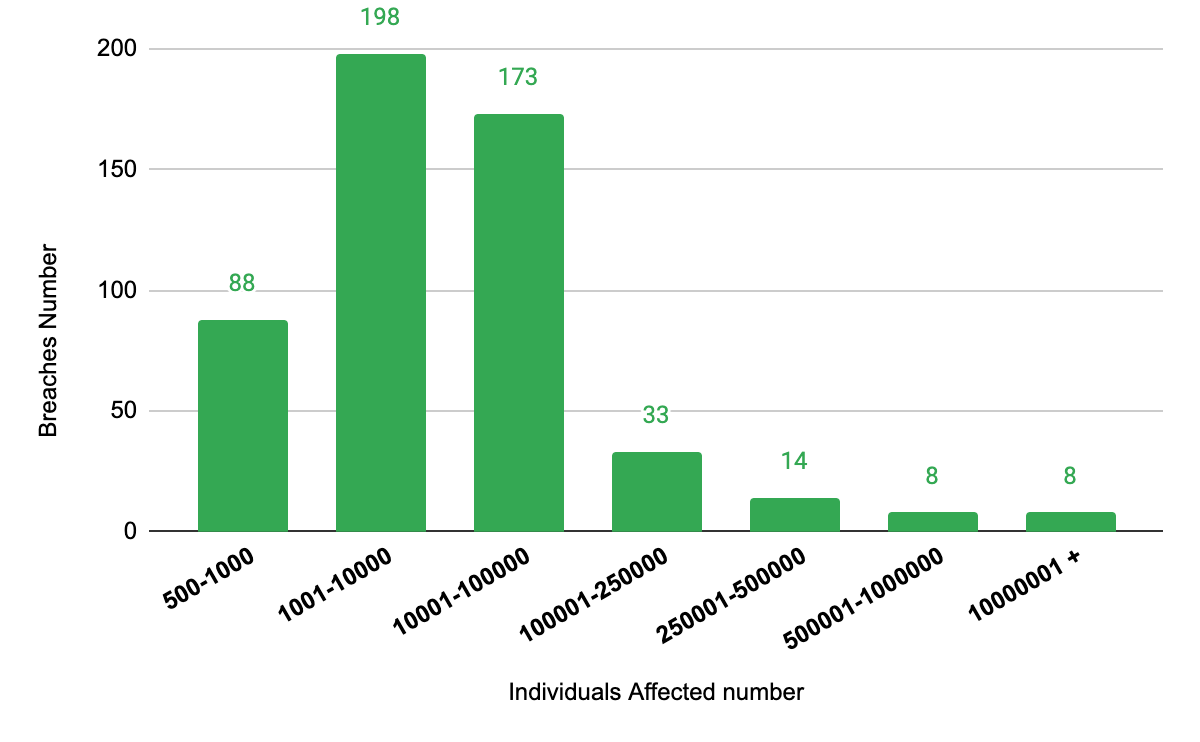
The number of reported breaches to the affected individuals
Among all the breaches 373 were reported by healthcare providers, 91 were reported by business associates, and 58 by health plan.
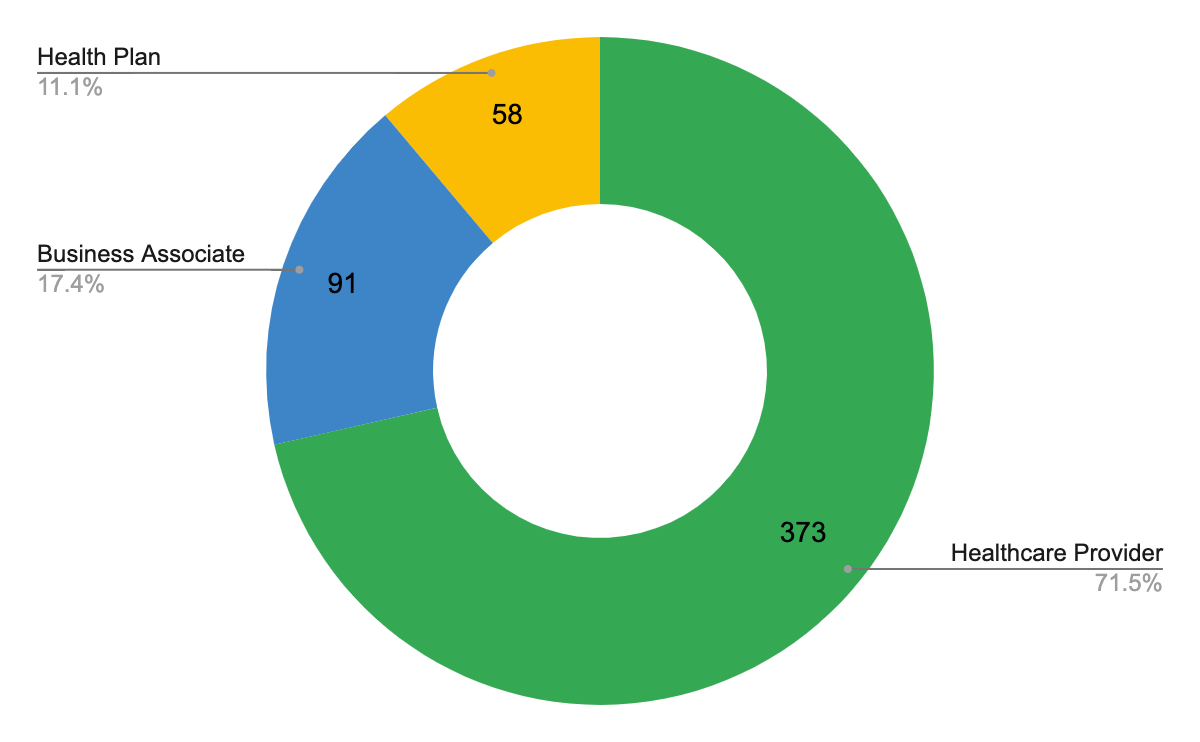
The number of breaches to entity type
Hacking/IT incidents happened in 419 of the 523 reports (78.9%), and Unauthorized Access/Disclosure accounted for another 71 of the reports (13,4%).
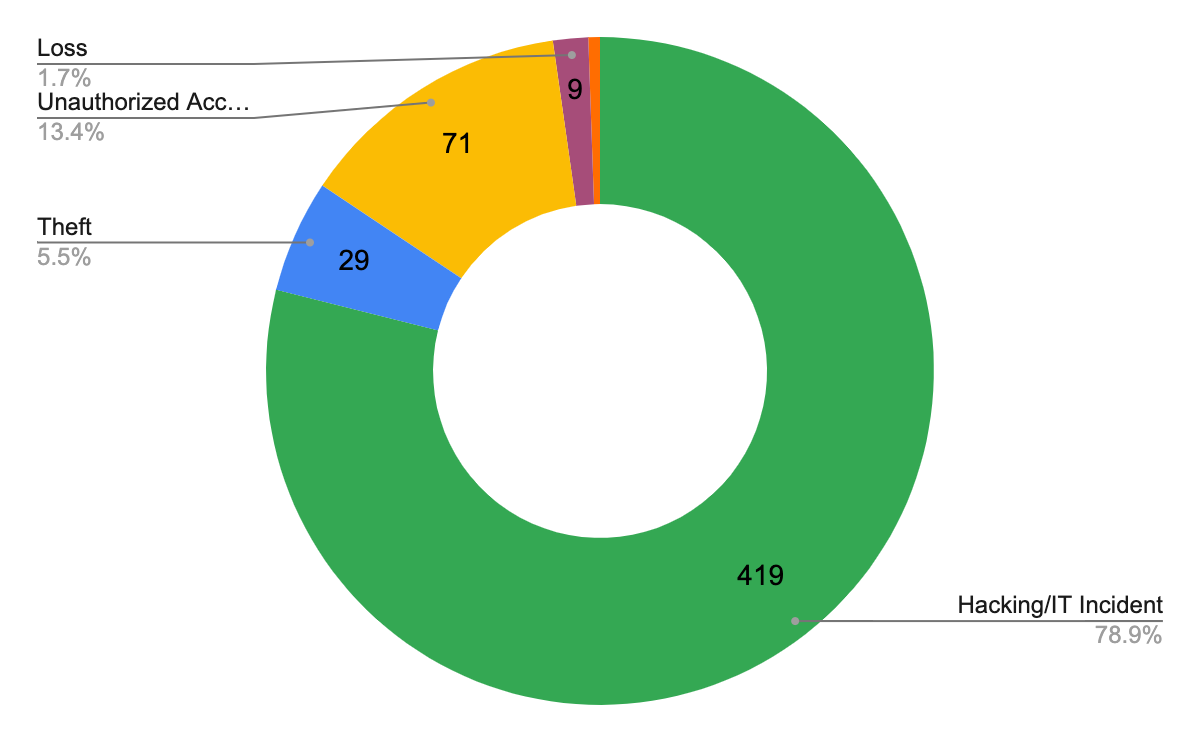
The number of breaches’ types
Here is a list of the most devastating (by number of affected individuals) cyber attacks this year so far according to the U.S. Department of Health and Human Services Office for Civil Rights.
OneTouchPoint, Inc.

Resource: OneTouchPoint, Inc.
OneTouchPoint, Inc. provides marketing services to health and medical providers. In April 2022, the company faced a proposed class action lawsuit over a data breach that supposedly exposed customer information held by a print and mailing service provider. OneTouchPoint claims it detected encrypted files on some of its systems on April 28 and immediately began an investigation into the incident. It later discovered that attackers accessed its network on April 27, but was unable to determine which files the attackers accessed on its network. It was originally reported that the data breach impacted on 1073316 individuals, and further it was announced about more than 2.6 million, and so far 4112892 individuals are known to have been affected. The compromised protected health information involves full names, addresses, ID numbers, dates of birth and social security numbers, medical and health assessment information, diagnosis codes, and description of services. This breach impacted about 40 organizations so far.
Advocate Aurora Health
Resource: Advocate Aurora Health
In the middle of October 2022 a non-profit health care system Advocate Aurora Health, in which there are 27 hospitals, disclosed a data breach that may have affected 3 million patients. The data leak was caused by the use of pixel technology (code fragments that collect information about users on certain websites or applications). Due to this technology, millions of patients’ health information may have been distributed with companies like Facebook and Google. This information includes IP address, dates, times, type, and locations of scheduled appointments, healthcare provider information, first and last names and medical record numbers (due to the using MyChart and LiveWell), insurance status, proxy account information. After the disclosure this system has since turned off or removed the pixels and launched an investigation into the case.
Shields Health Care Group, Inc.
Resource: Shields Health Care Group
On March 28, 2022 the U.S. medical services provider specializing in MRI and PET/CT diagnostic imaging, radiation oncology, and ambulatory surgical services Shields Health Care Group submitted that “Shields was alerted to suspicious activity that may have involved data compromise”. It affected 2 millions of individuals from 56 affiliated facilities providers, and according to the official notice, the breached protected health information included full name, Social Security number, date of birth, home address, provider information, diagnosis, billing information, insurance number and information, medical record number, patient ID, and other medical or treatment information from March 7, 2022, to March 21, 2022. Shields claims there has been no evidence that any of the stolen information has been used improperly or shared through unauthorized channels.
Professional Finance Company, Inc.

Resource: Professional Finance Company, Inc.
Professional Finance Company, Inc. is one of the leading debt recovery agencies and provides services for healthcare providers, retailers, financial organizations, and government agencies. On February 26, 2022, according to the company's breach notification, a ransomware attack was identified and blocked. During the attack an unauthorized intruder accessed some systems and obtained protected health information. The potentially accessed information included names, addresses, accounts receivable balances, information regarding payments made to accounts, dates of birth, Social Security numbers, health insurance information, and medical treatment information about 1918941 individuals of at least 24 clients. After the case, the company claims to have scoped and rebuilt vulnerable systems and taken steps to strengthen its network security.
Baptist Medical Center (Baptist Health System)

Resource: Baptist Health System
In April Baptist Medical Center and Resolute Health Hospital detected that their systems were infected by malicious code. An authorized intruder gained access to a business account from January 20 to August 12. This breached health information included Social Security numbers, driver's license numbers, state ID numbers, financial account information, treatment information, health insurance information, dates of service, and billings and claims information. Also, some data was removed from the system. The attack affected five hospitals in Texas and 1608549 individuals.
Practically after each cyber attack, it is stated that no evidence was found that the compromised information was used for purposes other than those for which it was intended. However, some of the compromised information does not appear for months or even years after the data breach incident, and at any time, this lost information can be used for social engineering, phishing, scamming, and even racketeering. Thus, it is necessary to be proactive, not to patch up the holes after the fact. And, first and foremost, this applies to the thoughtful choice of a service provider and software development company.
Categories
About the author
Share
Need a project estimate?
Drop us a line, and we provide you with a qualified consultation.






